Why Manufacturers Are Getting Denied Cyber Insurance
May 12, 2026

Executive Summary
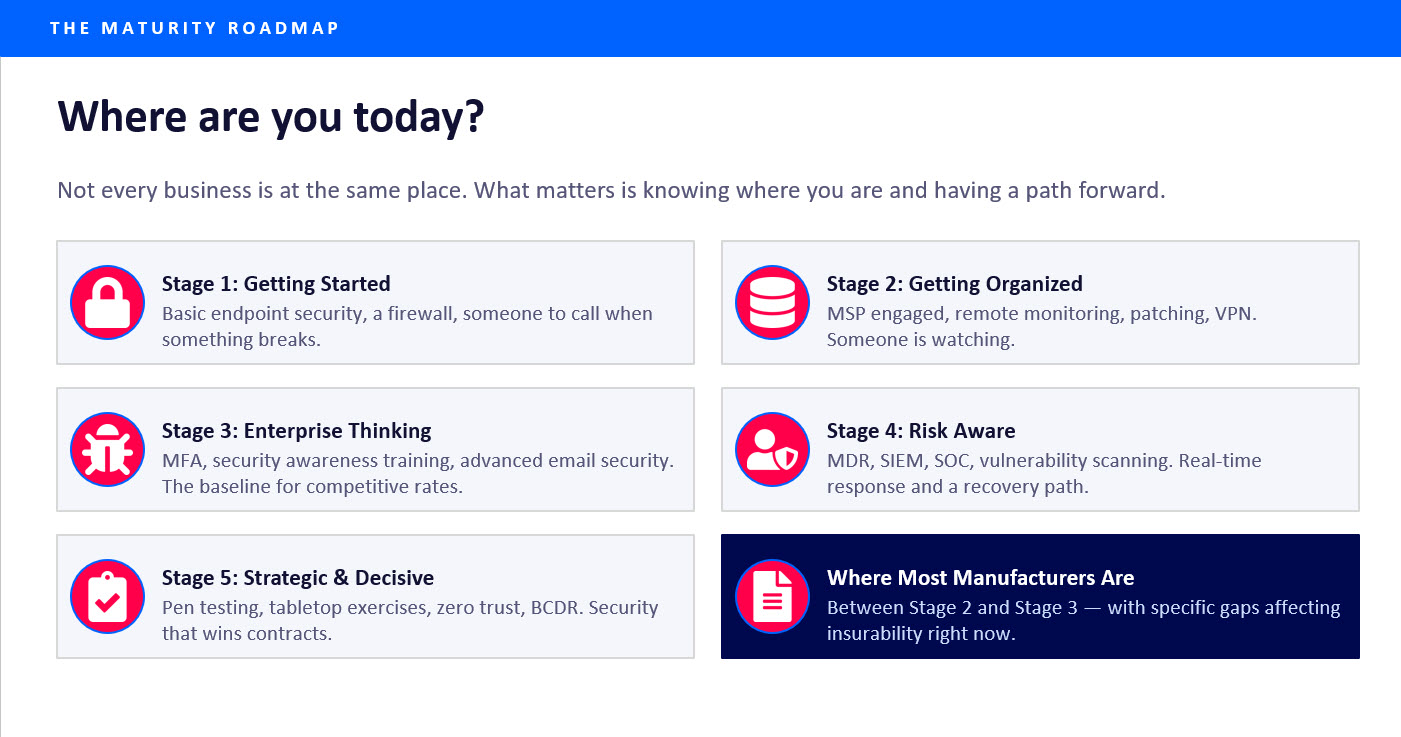
Cyber insurance underwriting has changed dramatically for manufacturers. What was once a relatively straightforward renewal process has evolved into a rigorous evaluation that examines operational resilience, identity security, backup integrity, and incident response readiness.
Manufacturers are increasingly being denied coverage, receiving higher premiums, or facing policy exclusions because insurers now view the sector as one of the highest-risk industries for ransomware and operational disruption. Legacy systems, industrial automation, robotics, operational technology (OT), and interconnected supply chains have created a larger and more complex attack surface than many companies realize.
At the same time, cyber insurers are demanding stronger security controls, including multi-factor authentication (MFA), endpoint detection and response (EDR), secure and tested backups, vulnerability management, network segmentation, incident response planning, and OT security visibility. Many manufacturers only discover cybersecurity gaps during policy renewals or after experiencing a cyber incident.
The good news is manufacturers can significantly improve both their cybersecurity posture and their insurability through proactive planning, risk assessments, and security modernization. This post explores why manufacturers are considered high-risk by insurers, how automation and robotics are increasing cyber exposure, what insurers are evaluating during underwriting, common reasons coverage is denied, and practical steps manufacturers can take to improve insurability.
Why Manufacturers Have Become High-Risk Targets
Manufacturing has become one of the most heavily targeted industries for cyberattacks, and cyber insurance carriers are responding accordingly. What used to be a simple insurance renewal now involves technical assessments, external vulnerability scans, and detailed security questionnaires. Manufacturers across the country are discovering that cyber insurance is no longer just a financial product. It has become a direct evaluation of cybersecurity maturity.
Cybercriminals target manufacturers because operational downtime creates immediate financial pressure. Unlike many office-based businesses, manufacturing environments depend on continuous operations. If production stops, companies can face delayed shipments, supply chain disruptions, lost revenue, contract penalties, safety concerns, and operational chaos. Attackers understand this urgency and often assume manufacturers are more likely to pay ransomware demands quickly to restore operations. As a result, manufacturing consistently ranks among the most targeted sectors for ransomware attacks worldwide.
Modern Manufacturing Is More Connected Than Ever
Manufacturing environments have changed dramatically over the past decade. Today's facilities increasingly rely on robotics, industrial automation, smart manufacturing systems, industrial IoT devices, cloud-connected operational technology, remote monitoring platforms, and vendor remote access tools. Companies involved in advanced automation are recognizing that cybersecurity and operational resilience must evolve alongside operational efficiency.
As robotics, automation platforms, and connected production environments continue to expand, insurers are paying much closer attention to how manufacturers secure operational technology environments.
Do Robots and Automation Increase Cyber Risk?
The short answer is yes, but not because robots themselves are inherently insecure. The real issue is that automation increases connectivity, complexity, and operational dependency. Modern robotic systems often integrate with production networks, ERP and MES systems, cloud dashboards, remote vendor support tools, industrial control systems, and third-party service providers. Every integration creates another potential attack path.
Many industrial robotic environments also rely on legacy operating systems, embedded software, proprietary protocols, and difficult-to-patch infrastructure. Because downtime is expensive, many companies delay updates or security changes that could interrupt production. That creates longer exposure windows for vulnerabilities. From an insurance perspective, highly automated environments can increase risk because operational interruptions become more severe when production relies heavily on interconnected systems.
The Growing OT and IT Convergence Problem
Historically, operational technology systems were isolated from corporate IT environments. That is no longer the case. Today, manufacturing environments frequently connect robotics, PLCs, sensors, HVAC systems, industrial control systems, and production management software to broader enterprise networks and cloud services.
This convergence creates significant cybersecurity challenges if segmentation and visibility are weak. A compromise in a traditional IT environment can potentially spread into operational systems if proper controls are not in place. Cyber insurers increasingly evaluate how manufacturers separate and secure OT and IT environments because of this risk. The role of SIEM in manufacturing environments is one practical way companies are gaining visibility across both IT and OT.
What Cyber Insurance Carriers Are Looking For
Insurance underwriters now expect manufacturers to demonstrate measurable cybersecurity maturity. Applications that once focused on basic security controls now require technical validation and operational evidence. The most heavily scrutinized areas include the following.
Multi-factor authentication. MFA has become one of the most important underwriting requirements. Most insurers now expect MFA to be enforced for email access, VPN connections, administrative accounts, remote access platforms, and cloud applications. Companies without strong MFA implementation may be denied coverage outright.
Endpoint detection and response. Traditional antivirus software is no longer considered sufficient. Insurers increasingly expect advanced EDR solutions capable of behavioral threat monitoring, ransomware detection, centralized visibility, incident investigation support, and automated response capabilities.
Secure and tested backups. Backups are no longer just about storing copies of data. Insurers want to know whether backups are immutable, whether they're segmented from production systems, whether they're regularly tested, and how quickly operations can recover. Manufacturers that cannot demonstrate reliable recovery procedures face increased underwriting concerns.
Vulnerability management. Manufacturers are frequently flagged for unpatched systems, internet-facing vulnerabilities, unsupported software, and incomplete remediation processes. Insurers increasingly expect continuous vulnerability scanning and documented patch management procedures.
Incident response planning. Underwriters increasingly ask whether a documented incident response plan exists, whether it's been tested, who manages decision-making during an incident, and how operations will recover. Tabletop exercises and recovery testing are becoming critical indicators of organizational maturity.
Why Claims Sometimes Get Denied
One of the biggest misconceptions in the market is that having cyber insurance automatically guarantees coverage. In reality, insurers often investigate whether required controls were actually implemented as stated during underwriting. Claims can become problematic if companies misrepresented security controls, failed to deploy required protections, did not fully implement MFA, had ineffective backup procedures, or ignored known vulnerabilities.
Many manufacturers only discover hidden security gaps during a claim investigation. That's why cybersecurity readiness must go beyond simply completing an application. The controls you attest to must match your real-world environment. For a deeper look at what insurers are actually checking and what voids coverage, see Cyber Claims Get Denied If Your Controls Are a Mess.
How Manufacturers Can Improve Their Insurability
Manufacturers can dramatically improve both their cybersecurity posture and their insurance eligibility through proactive planning. A cybersecurity risk assessment is typically the right starting point, helping identify security gaps, operational risks, insurance concerns, vulnerability exposure, and OT security weaknesses.
Strengthen identity security. Identity-based attacks remain one of the leading causes of ransomware incidents. Manufacturers should prioritize MFA deployment, privileged access management, strong password policies, access reviews, and removal of stale accounts.
Improve OT segmentation. Separating operational technology from traditional IT systems can significantly reduce risk. Strong segmentation helps limit ransomware spread, improve operational resilience, reduce production impact, and increase visibility and control. For manufacturers with defense contracts, CMMC compliance builds toward the same segmentation and access control requirements insurers expect.
Secure vendor access. Third-party remote access is one of the most common attack vectors in manufacturing environments. Companies should require MFA for vendors, limit persistent remote access, monitor sessions, enforce least-privilege access, and review vendor permissions regularly.
Test recovery procedures. Manufacturers should regularly validate backup integrity, recovery speed, business continuity plans, incident response workflows, and communication procedures. Recovery testing demonstrates operational maturity to insurers and improves resilience during real-world incidents.
Cyber Insurance Is Becoming a Security Audit
Cyber insurance underwriting is no longer just about transferring financial risk. It has become a direct evaluation of operational cybersecurity maturity. Insurers now want proof that manufacturers can prevent attacks, detect threats quickly, recover operations efficiently, maintain business continuity, and protect operational environments.
The manufacturers best positioned for the future will be the ones that treat cybersecurity as part of operational engineering, not simply an IT function. The Taylor Turning case study is a practical example of how a Michigan manufacturer addressed security gaps, improved its posture, and built toward compliance in a short timeframe.
Join the Conversation
At 11 a.m. on May 20, 2026, the Michigan Manufacturers Association will host a discussion featuring STACK Cybersecurity Founder and CEO Rich Miller and cybersecurity insurance specialist Jake Charen. The session will cover why cyber insurance underwriting is tightening, common reasons manufacturers lose coverage, how automation and OT environments affect risk, what insurers are evaluating today, and practical steps companies can take before renewal season. Register through the Michigan Manufacturers Association. For additional resources on manufacturing cybersecurity and compliance, visit the STACK Manufacturers Resource Hub.
Frequently Asked Questions
Why are manufacturers considered higher cyber risks than other businesses?
Manufacturers are heavily dependent on continuous operations. A cyberattack can immediately halt production, disrupt supply chains, and create significant financial losses. Because downtime is so costly, ransomware groups often target manufacturers specifically.
Are robots and automation making manufacturing less secure?
Not inherently, but automation increases connectivity and operational dependency. Modern robotics often connect to cloud platforms, production systems, and remote vendor tools, which expands the attack surface. Without proper segmentation and security controls, automated environments can become more vulnerable to cyber incidents.
Why are insurers focusing more on operational technology?
OT systems control physical manufacturing operations, including robotics, production lines, industrial sensors, and PLCs. If these systems are compromised, the impact can extend beyond data loss and potentially disrupt physical operations, safety, and production continuity. Insurers view OT environments as high-impact risk areas.
What security controls are most important for cyber insurance approval?
Most insurers now expect MFA deployment, EDR solutions, secure and tested backups, vulnerability management, incident response plans, network segmentation, and vendor access controls. These controls are increasingly viewed as baseline requirements, not differentiators.
Can a cyber insurance claim be denied after an incident?
Yes. Claims may be denied or reduced if required security controls were not fully implemented or if information provided during underwriting was inaccurate. Companies must ensure their documented controls match their real-world environment.
Why is MFA so important to insurers?
MFA helps prevent credential-based attacks, which remain one of the most common ransomware entry points. Insurers increasingly require MFA for email, VPNs, administrative accounts, remote access systems, and cloud platforms.
How does remote vendor access increase manufacturing risk?
Many manufacturers allow vendors and integrators remote access to production systems for maintenance and support. If these connections are poorly secured, attackers can exploit them to gain access into the environment. Weak vendor access controls are a common issue during underwriting reviews.
Are legacy systems a major issue for manufacturers?
Yes. Many manufacturing environments still rely on unsupported operating systems, older industrial control systems, and specialized software that is difficult to patch. These systems often remain vulnerable longer because operational downtime limits maintenance opportunities.
What should manufacturers do before cyber insurance renewal season?
Manufacturers should conduct cybersecurity assessments, review underwriting requirements, validate MFA implementation, test backups and recovery plans, improve OT segmentation, review vendor access controls, and document security processes. Starting early gives companies time to remediate issues before underwriting reviews begin.
Is cyber insurance enough to protect manufacturers?
No. Cyber insurance helps manage financial risk, but it does not prevent attacks or operational disruption. Strong cybersecurity practices remain essential for protecting manufacturing operations, maintaining resilience, and reducing business risk.
Work with STACK
If your business wants to understand its exposure or build stronger defenses, email info@stackcyber.com or call (734) 744-5300.
