Cyber Insurance for Manufacturers: Controls That Protect Your Coverage
May 8, 2026

A ransomware attack hit a parts manufacturer over Memorial Day weekend. The hackers didn't wait for business hours. By the time staff returned Tuesday morning, fraudulent emails had already gone out to suppliers, vendors, and clients requesting payment. Systems were locked. The shop floor was idle. Customer calls were going unanswered.
The company filed a claim under its cyber liability insurance policy. It covered exactly this kind of event: breach response, forensic investigation, lost income, the legal exposure from those fraudulent payment requests sent to everyone they did business with. The carrier denied it anyway. Not over fine print or a policy exclusion. Incomplete firewall logs and untested backups were enough to void the coverage. Three years of premiums, and the company faced the full cost alone.
Download the STACK Cybersecurity Cyber Liability Insurance Checklist
What is Cyber Insurance?
Cyber insurance is designed to protect businesses from the financial consequences of cyber incidents, such as ransomware, data breaches, and business email compromise. It helps you recover without bearing the full burden of the damages. Depending on your coverage, it can help pay for data recovery, legal fees, regulatory fines, customer notification, credit monitoring, and even business interruption costs. Some policies may also cover ransom payments, but that varies.
This type of coverage is more than a safety net. It's a financial cushion that helps your business survive and recover. But qualifying for it isn't automatic. Your IT strategy plays a major role in getting coverage and staying covered.
Role of IT Strategy
Your cyber policy is only as good as the security behind it.
With cyberattacks increasing in frequency, scale, and complexity, insurers are tightening their requirements. Getting cyber insurance today is a lot harder than it was even a year ago.
Manufacturers have enough to worry about without adding a denied insurance claim to the list. But that's exactly what happens when a business buys a cyber liability policy, assumes it's covered, and never connects the policy to the actual state of its security controls.
Manufacturers who get the most out of their coverage understand insurers underwrite what they can verify. They aren't in the business of paying claims when the controls you said you had weren't actually in place.
Business Pressures Create Problems
Most manufacturers are squeezed right now. Prices haven't moved. But labor, materials, and overhead have. When margins shrink, IT spend often gets cut first. It's a defensible short-term decision. The quarterly numbers look better.
The long-term math is brutal. Security gaps that open quietly today become incidents that close operations for weeks. Production disruption, supply chain strain, and customer relationship damage stack on top of whatever the breach itself cost. The money saved on IT spend rarely covers the first day of recovery, let alone the full event.
Cyber insurance exists partly to absorb that cost. But it only works if you've done the underlying work.
Three Questions
The ransomware supplemental questionnaire insurance carriers now require maps to a control that either raises or lowers the probability of a claim. Insurers have the loss data. They know exactly which gaps correlate with incidents, and they price and underwrite accordingly.
Three questions summarize what every underwriter wants to know before issuing a policy.
1. Can you detect an attack? This means active monitoring, endpoint protection, and alerting, not a firewall someone set up years ago and hasn't touched since. Detection capability is what separates businesses that catch threats early from businesses that find out about a breach weeks after it started.
2. Can you recover? A tested, off-site backup and a documented incident response plan are the answer here. Not a backup that runs automatically and has never been verified. Not a response plan that exists in someone's head. Carriers want to see that recovery has been practiced, not just theorized.
3. Can you prove it? This is where many businesses get caught. They've been doing reasonable things for years but have no documentation to show for it. Logs, training records, written policies, evidence of testing. If none of it is documented, the carrier's position in a claim review is that it didn't happen.
Security Gaps
Gaps in your security posture can void coverage on a policy you've been paying into for years. If you represented on your application that multi-factor authentication (MFA) was enabled and a claim review finds it wasn't consistently enforced, the carrier has grounds to deny the claim.
This reflects the same logic that applies to any insurance product. Misrepresentation of risk, even unintentional misrepresentation, affects coverage. Manufacturers who go through a coverage review before their next renewal, rather than after an incident, are the ones who avoid that situation.
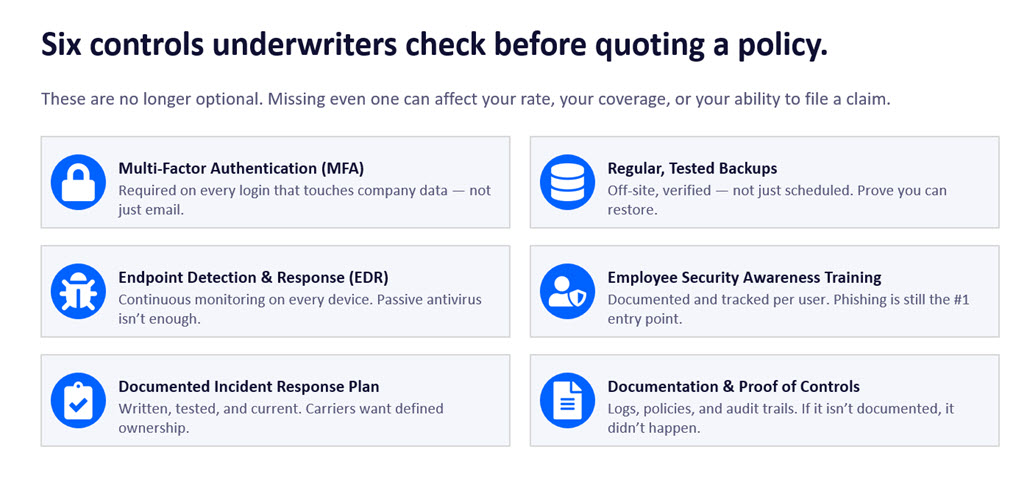
Controls That Matter Most
Four controls come up repeatedly in claim reviews as the difference between a paid claim and a denied one.
Multi-factor authentication on every login that touches company data. Not just email. Every system, every remote access point, every administrative account. MFA is the single most effective control against credential-based attacks, which remain the most common entry point for ransomware.
Endpoint detection and response (EDR) on every device. Continuous monitoring, not periodic scans. EDR gives security teams visibility into what's happening across the environment in real time. It's what makes early detection possible.
Tested, off-site backups. The word "tested" is doing a lot of work there. A backup that hasn't been verified is a theory. Carriers want to know recovery has been demonstrated, not just scheduled.
Documented security awareness training, tracked per user. Phishing is still the most common way ransomware gets into a manufacturing environment. Training that is documented and tracked per employee demonstrates due diligence and gives insurers something concrete to point to when evaluating a claim.
Businesses that have all four of these in place typically see meaningfully better rates than comparable businesses missing any of them. Some carriers won't quote without them.
Manufacturing Risk Profile
Manufacturers face a specific risk profile that insurers understand well. Operational technology environments often include legacy systems that were never designed to be internet-connected but now are. Shop floor networks that aren't segmented from corporate networks mean a ransomware infection that starts on an administrative laptop can spread directly to production systems. And that scenario creates multi-week or month outages.
For manufacturers with defense contracts, CMMC compliance is an approaching reality, not a distant concern. Building toward CMMC also closes most of the gaps insurers care about. The frameworks reinforce each other, and the investment serves both purposes.
"Manufacturers often come to us after a renewal conversation where the carrier either raised rates significantly or asked questions they couldn't answer," said Rich Miller, Founder and CEO of STACK Cybersecurity. "The controls that matter to insurers are the same ones that reduce risk. Getting those in place before renewal, not after an incident, is where the real value lies."
Understand Your Coverage
Not all cyber policies are structured the same way. The difference between first-party and third-party coverage matters more than most business owners realize until they're filing a claim.
First-party coverage protects your own business after an incident. It typically covers legal counsel to determine your notification and regulatory obligations, recovery and replacement of lost or stolen data, customer notification and call center services, lost income due to business interruption, crisis management and public relations costs, cyber extortion and fraud, forensic investigation fees, and fines or penalties related to the incident. For a manufacturer facing a ransomware attack, this is the coverage that keeps operations from going under while recovery is underway.
Third-party coverage handles liability when outside parties bring claims against you. It generally covers payments to consumers affected by a breach, settlement expenses from disputes or lawsuits, losses related to defamation or intellectual property claims, costs for litigation and responding to regulatory inquiries, and accounting costs. For manufacturers handling customer data or operating within a supply chain, third-party exposure can be significant. A breach that affects a partner or downstream customer creates liability that first-party coverage alone won't address.
Both types of coverage come with limits, exclusions, and sub-limits that vary by carrier and policy. Review them carefully before signing, ideally with a cybersecurity adviser who can flag gaps between what the policy covers and what your actual risk profile looks like.
Where Do IT Service Providers Fit?
When it comes to cyber insurance, IT service providers like STACK Cybersecurity play a vital role. You're not expected to navigate the technical requirements alone.
Most businesses struggle to translate insurer requirements into clear, actionable steps. A good IT service provider bridges that gap by making sure your systems and processes meet the bar insurers set, helping you qualify for coverage in the first place.
Once you're covered, they work to keep you that way: setting up tools like MFA, running employee training, and implementing routine backups so you're never caught off guard at renewal. And if an incident does occur, your provider helps minimize the damage. The faster you respond and recover, the more likely your claim will be accepted and the less impact your business will feel.
Whether it's strengthening your posture, documenting proof, or supporting fast recovery, the right partner helps you meet insurer demands without derailing daily operations.
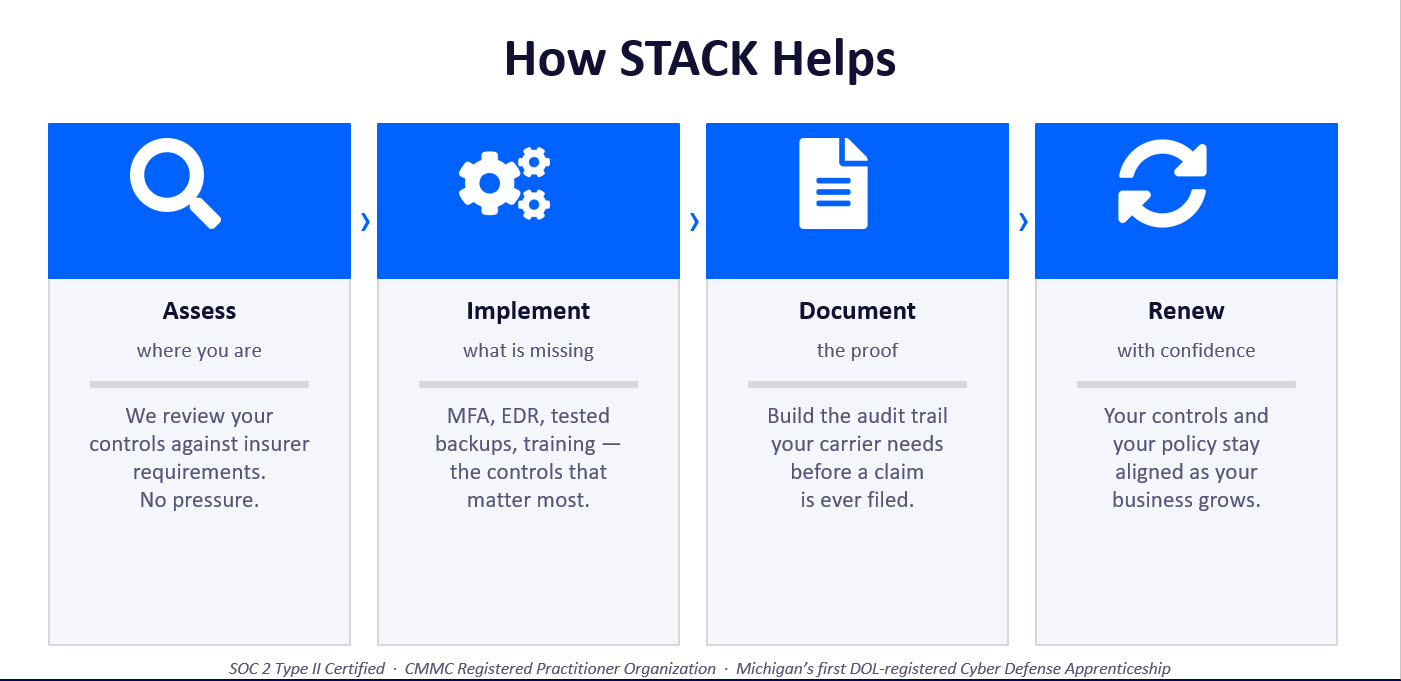
STACK Gets You Insurable
As a trusted IT service provider, we'll support your business beyond basic IT and help you build a foundation that cyber insurers trust and reward. We'll start by assessing your environment and identifying what's missing, from MFA and antivirus to policy documentation and employee training. Then, we'll tailor solutions that align with both your business goals and insurer expectations. We'll also go beyond implementation and make sure everything is documented and audit-ready, because paperwork is just as important as protection.
Email: info@stackcyber.com
Phone: (734) 744-5300
Contact Form
