HIPAA Isn't Enough for Assisted Living Compliance
Feb. 17, 2026

For many assisted living and behavioral health providers, compliance conversations start and end with the Health Insurance Portability and Accountability Act, commonly known as HIPAA. The assumption is understandable. HIPAA is the best-known health data regulation in the country, and it carries real penalties for noncompliance.
But that assumption is also where the real risk begins.
Across assisted living, adult foster care, homes for the aged, and behavioral health facilities, cybersecurity incidents are increasingly occurring outside the narrow scope HIPAA was designed to address. Providers that believe they are "covered" because they have completed HIPAA training or signed a business associate agreement often discover too late that compliance is broader, messier, and more operational than they were led to believe.
HIPAA matters. It just isn't enough.
What HIPAA Actually Covers
HIPAA was designed to protect protected health information. Its Security Rule focuses on safeguarding electronic health data through administrative, physical, and technical controls. That framework is important, but it's intentionally limited in scope.
HIPAA doesn't govern payroll systems, email platforms, vendor portals, remote access tools, or most financial workflows. It doesn't address business email compromise, fraudulent wire transfers, payroll diversion, or vendor credential theft. Yet those are the incidents most often disrupting assisted living operations.
This distinction matters because attackers aren't targeting assisted living providers for sophisticated clinical systems. They're targeting the simplest, most profitable points of entry: email accounts, password reuse, vendor access, and payroll changes. Those incidents can halt paychecks, freeze accounts, drain operating funds, and erode staff trust long before a single medical record is touched.
A facility can be fully attentive to HIPAA and still be exposed everywhere hackers actually operate.
The Real Attack Surface in Assisted Living
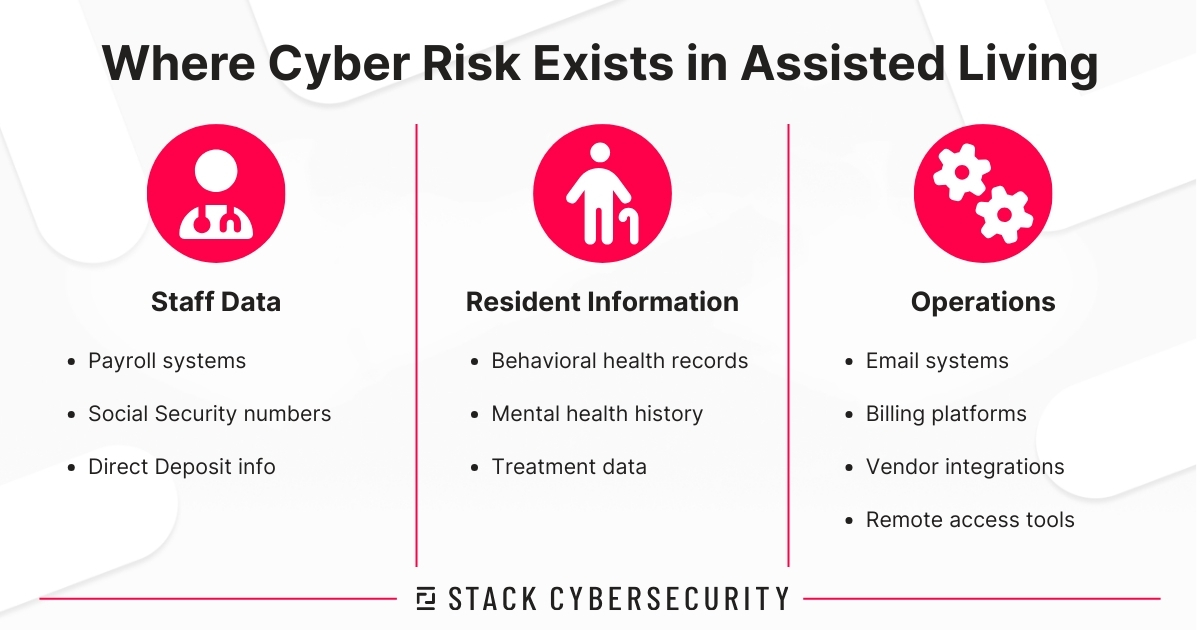
To understand the compliance gap, it helps to look at what is truly at stake for assisted living and behavioral health providers.
First, there is staff data. Human resources systems contain Social Security numbers, direct deposit information, tax records, and personal identifiers. Payroll fraud and impersonation attacks are increasingly common because staff data is valuable and often poorly protected.
Second, there is resident information. Behavioral health records, mental health histories, and substance use treatment data carry long-term consequences if exposed. Unlike a credit card number, this information cannot be replaced. The harm is personal and permanent.
Third, there are operations. Email systems, billing platforms, backups, remote access tools, and vendor integrations keep facilities running. When those systems are disrupted, care delivery, reimbursement, and staffing stability suffer immediately.
These systems sit largely outside HIPAA's narrow definition of protected health information. They're still central to safety, trust, and continuity.
Compliance Obligations That Exist Beyond HIPAA
HIPAA is only one layer of responsibility. Assisted living providers also operate under state licensing expectations, contractual obligations, and consumer protection rules that rarely get the same attention.
State oversight bodies expect providers to operate safely, responsibly, and with reasonable safeguards in place. While requirements vary, licensing consequences don't disappear simply because an incident didn't involve clinical records.
Contracts create another major compliance blind spot. Vendor agreements, payer contracts, cyber insurance applications, and business associate agreements often include security requirements, breach notification timelines, and liability language that facilities don't fully review until something goes wrong. When a vendor is breached, providers are often surprised to learn how much responsibility still falls on them.
Compliance is inherited through contracts whether facilities acknowledge it or not.
When the Federal Trade Commission Enters the Picture
Many assisted living providers don't realize the Federal Trade Commission (FTC) Safeguards Rule applies to them. Issued under the Gramm-Leach-Bliley Act, the Safeguards Rule applies to businesses that handle certain types of consumer financial information. The rule depends on what the business does. Billing operations, payment plans, consumer financial data, and third-party processors can all trigger obligations under the rule.
When it applies, the Safeguards Rule requires a written information security program with administrative, technical, and physical safeguards appropriate to the company's size, complexity, and risk. That expectation looks much closer to a comprehensive cybersecurity program than to a checklist.
HIPAA may not be the standard used to judge a financial incident. Many providers don't learn that until regulators or insurers are already involved.
Third-Party Risk
Assisted living facilities depend heavily on vendors. Managed service providers, electronic health record platforms, billing services, training portals, and software providers all touch sensitive systems and data.
Third-party breaches are not hypothetical. They are a common source of real-world incidents. Yet vendor security is often treated as someone else's responsibility. Facilities assume certifications or assurances are enough without clarifying access controls, breach notification responsibilities, or liability exposure.
When a vendor is compromised, the operational impact still lands on the provider. Staff lose access. Residents experience disruption. Leaders answer difficult questions from boards, regulators, and families.
Vendor risk is provider risk.
What a Practical Baseline Looks Like
Closing the compliance gap does not require building a hospital-grade security team. It requires aligning controls with real-world risk.
That starts with fundamentals: multifactor authentication on email and remote access, password managers to eliminate reuse, advanced email filtering, and regular staff security awareness training that goes beyond annual compliance videos. Clear incident reporting procedures that encourage early reporting instead of blame also play a critical role.
It also requires understanding risk before trying to fix it. A structured cybersecurity risk assessment that looks at people, systems, and data provides clarity. It replaces assumptions with evidence and allows leaders to prioritize improvements that actually reduce exposure.
Most importantly, it requires a mindset shift. Compliance is not a single rule or certification. It's the sum of regulatory obligations, contracts, operational reality, and reasonable safeguards.
Align Cybersecurity, Compliance
HIPAA compliance is not the same as operational safety.
If your protections focus on data classifications but ignore email, payroll, vendors, and access controls, you still have a compliance gap. And that gap is where attackers are most likely to strike.
Assisted living providers care deeply about their staff and residents. Aligning cybersecurity and compliance with how facilities actually operate is part of delivering safe, reliable care in an increasingly digital environment.
Want to Close the Compliance Gap?
STACK Cybersecurity works with assisted living providers to identify real-world risk, strengthen operational controls, and build security programs that go beyond basic compliance. Call (734) 744-5300 or Contact Us to start the conversation.